Starting March 15, 2026, new rules for SSL/TLS certificates will take effect. The maximum validity period will be reduced almost by half. Previously a certificate could be valid for up to 398 days, but the new limit will be 200 days.
The changes were approved by the CA/Browser Forum, an industry organization that defines security standards for certificate authorities and browser developers.
In practice, this means that the validity period of SSL certificates will gradually become shorter and certificates will need to be renewed more frequently.
Let’s look at what exactly is changing and whether website owners need to take any action.
If your website does not yet use SSL, you can use a free Let’s Encrypt certificate or a commercial certificate with extended validation. More information about available options can be found on the SSL certificates page.
What will change?
The main change concerns the maximum validity period of SSL certificates.
The transition will happen gradually:
| Date | Maximum SSL validity period |
|---|---|
| Before March 15, 2026 | 398 days |
| From March 15, 2026 | 200 days |
| From March 2027 | 100 days |
| From March 2029 | 47 days |
As a result, the industry will gradually move from annual certificates to certificates that are valid only for a few weeks.
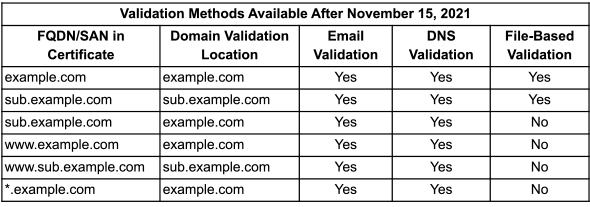
The reuse period for domain validation will also be shortened. This means certificate authorities will verify domain ownership more frequently.
Why is the SSL validity period being reduced?
The main reason is improving internet security.
The longer a certificate remains valid, the more time attackers have if a private key is compromised or a configuration error occurs. Shorter validity periods allow potentially vulnerable certificates to be replaced faster.
There are also other reasons:
- faster transition to new cryptographic algorithms
- more frequent domain ownership verification
- preparing infrastructure for future security standards
Will SSL certificates need to be purchased more often?
No. Shorter certificate lifetimes do not mean higher costs.
Commercial certificate authorities already use a subscription model. This means a certificate can be purchased for 1 or 2 years, while it may be reissued several times during that period at no additional cost.
For example:
- a certificate is purchased for one year
- the first certificate is valid for about 200 days
- a new certificate is then issued for the remaining period
This process is called reissue and is a standard practice.
What does this mean for website owners?
The main practical change is that certificates will need to be renewed more often.
Approximate renewal frequency:
- in 2026 — about two renewals per year
- in 2027 — three or four renewals
- after 2029 — renewals may happen every few weeks
If SSL certificates are installed manually, the risk of forgetting to renew them will increase.
Why automatic SSL renewal is becoming the standard
Modern web infrastructure increasingly relies on automation.
If a certificate expires, browsers begin displaying security warnings. This can lead to loss of visitors and reduced trust in the website.
For this reason, most hosting platforms now use automated SSL management.
For example, free Let’s Encrypt certificates can automatically:
- be issued
- be installed on the server
- be renewed before expiration
On web hosting plans, these certificates are usually enabled through the control panel and renewed automatically.
Do hosting clients need to do anything?
In most cases, no.
If you are using a free Let’s Encrypt SSL certificate through the hosting control panel, it will be issued and renewed automatically without any action from the website owner.
Commercial SSL certificates (for example, OV or EV) usually require manual installation and periodic reissuance. Their validity period will also be shortened according to the new industry rules.
When should you pay attention?
You should check your SSL configuration if:
- the certificate is installed manually on the server
- commercial OV or EV certificates are used
- certificates are managed within corporate infrastructure
In these cases it is recommended to configure automatic certificate renewal in advance.
Frequently asked questions
Why is the SSL validity period being shortened?
The goal is to improve security. Shorter certificates reduce risks if a key is compromised or cryptographic algorithms become outdated.
Will I need to pay for SSL more often?
No. Commercial certificates are usually purchased for one or two years and may be reissued multiple times within that period without additional cost.
What happens if an SSL certificate expires?
Browsers will display a security warning. Visitors may not open the website and search engines may reduce trust in the site.
Do hosting users need to take any action?
If you are using a free Let’s Encrypt SSL certificate through the hosting control panel, it is renewed automatically and requires no action.
Summary
Starting in March 2026, the maximum validity period of SSL certificates will be reduced to 200 days. In the future the validity period will become even shorter.
This is part of a global shift toward more frequent certificate renewal and automated security management.
For most website owners these changes will be almost invisible, especially if SSL certificates are managed through the hosting control panel.
Need an SSL certificate for your website?
Our hosting allows you to use free Let’s Encrypt certificates with automatic renewal as well as commercial certificates for projects that require extended validation.